Claudethe artificial intelligence of Anthropicis becoming more and more popular. According to some estimates, it reached 290 million monthly visits. This has made the model a very attractive target for cybercriminals. Security researchers from Malwarebytes have identified a counterfeit website that closely imitates the official Claude portal and which promises to install a seemingly legitimate version of the applicationwith the aim of distributing a malware-infected installation package. Whoever downloads the file actually receives a working copy of the application, but one is installed in parallel chain of malicious components that allows hackers to remotely access the device. In the next paragraphs we will therefore see how the attack works and how to avoid it.
How Claude Pro’s attack works
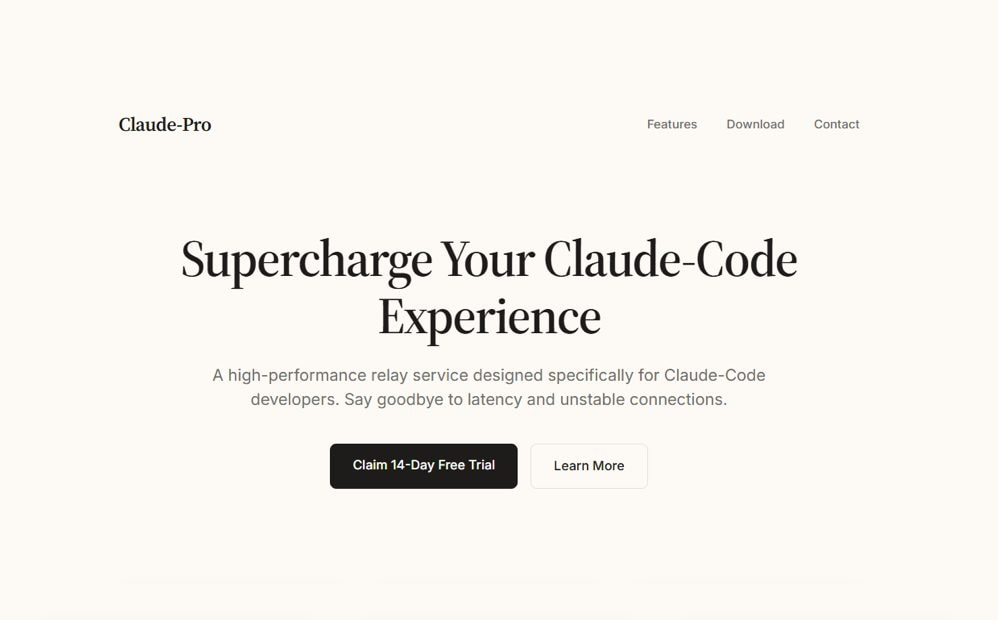
The fraudulent site looks like a Web page apparently belonging to Anthropicthe company that develops Claude, and which promises to download a “Pro” version of Claudeenclosed in the file Claude-Pro-windows-x64.zip. DNS records – the system that associates domain names with IP addresses – show that the domain has an active infrastructure forsending mass emailssuggesting that the attack also propagates via phishing messages. Once extracted, the archive contains an installer that you place in the path C:Program Files (x86)AnthropicClaudeCluade. Notice anything strange? There is a typo in the path (“Clwowde” instead of “Claude”), which represents a first warning sign.
The installation creates a shortcut on the desktop that, on the first click, launches one automatic script. This script runs the legitimate, working Claude application in the foreground, so as not to arouse suspicion, and simultaneously copies three files to a system startup folder in the background: NOVUpdate.exe, avk.dll And NOVUpdate.exe.dat.
The mechanism underlying the attack is deliberately difficult to unmask: the malware relies on completely legitimate software components – in this specific case, elements attributable to an antivirus program – to camouflage themselves within the system and escape Windows’ automatic checks. Neither the user nor the PC security tools therefore have immediate reasons to become suspicious.
In light of these considerations, it seems clear what the objective of the cyber criminals behind the attack is: to open a permanent access door to the victim’s device without them realizing it. In this way, whoever manages the attack can issue commands remotely, steal sensitive information or have the system download additional malicious components without anything being visible on the screen.
How to tell if your PC is infected
To check if your computer was involved in the attack, in addition to thinking about it and trying to remember if you have downloaded “strange” versions of Claude on your PC, you can check for the presence of NOVUpdate.exe files, avk.dll or NOVUpdate.exe.dat in the autostart folder Startupslook for the incorrectly named folder “Cluade” along the way C:Program Files (x86)AnthropicClaude and perform one full scan with updated anti-malware. If successful, the researchers of Malwarebytes suggest immediately disconnecting from the Internet and changing the passwords of all accounts used on that device.
Preventing the infection is much simpler than eradicating it: just limit yourself to download Claude exclusively from the platform’s official websiteavoiding links from emails, advertisements or sponsored search engine results. And this defense strategy obviously applies to any other software.